The world of work is constantly changing. If you look back at the last 20 years, you’ll realize by just how much. Fax machines, file cabinets and long days in the office are mostly a thing of the past. Now, people work from anywhere, on any device, at any time. Technology, of course, is the driving force […]

SASE: delivering healthcare to the edge?
Healthcare providers, hospitals and medical institutes have rapidly evolved over the last 18 months. While digitalization was already a focus in this sector, the pandemic forced organizations everywhere to press hard on the accelerator. As Satya Nadella famously said, organizations worldwide saw “2 years of digital transformation in 2 months.” Healthcare, though, is extra unique within […]

What makes a good security engineer? 7 traits to look for when hiring
So, you’ve started the process of hiring a security engineer. Your job ad is live, and you’ve already received a few resumes. As you begin to line up your interviews, you’re wondering how you’ll know when you’ve found the right candidate. The right security professional needs to be more than an excellent cultural fit. They […]

Hiring a compliance analyst? 5 traits to look for
A good compliance team can make the difference between a company that is successful vs not. Risks related to reputation, enterprise, technology, people, third party are just some of the areas that a compliance team gets involved in. Finding the right candidate is challenging but keeping these traits in mind can help look for good […]
Twitch Data Leak – What Happened? (Hint: Unpaid Privacy Debt)
Twitch, the live-streaming platform from Amazon, recently announced that it suffered an enormous data breach that exposed the company’s source code, users’ income streams and more. The breach was posted on the message board 4chan, a popular hacker forum. Worryingly, the hacker’s post suggested that this leak was just the start. It labelled the post […]

Webinar: protecting against ransomware: healthcare edition (4 takeaways)
In honor of cybersecurity month in the US and Europe, Polymer’s CEO, Yasir Ali, recently spoke in a webinar about the growing prevalence of ransomware attacks – and how hospitals, medical providers and other healthcare organizations can protect themselves. Here are 4 Key Takeaways: Takeaway 1: Ransomware is as scary as it sounds Not to […]

Cloud security challenges of privacy policy management
Becoming data-driven is a critical priority for organizations of all shapes and sizes. Data, combined with analytics, equals insights – and these insights can form the basis of predictions, better customer relationships and informed decisions. However, in the modern world, generating data insights comes with great responsibility. A lot of data, after all, relates to […]
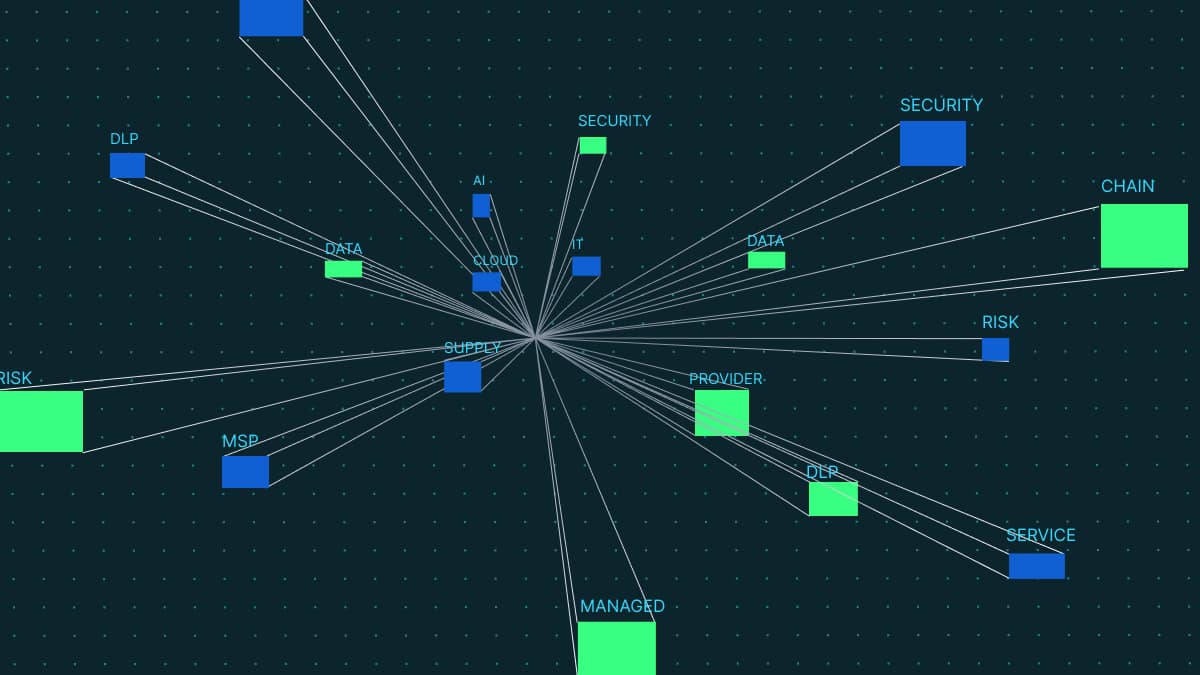
Top 7 DLP fails
Data loss prevention (DLP) is meant to do exactly what it says on the tin: prevent data loss. For today’s enterprises, this is a huge concern. Who doesn’t want to protect their reputation, assets, and bottom line from the fallout of a data breach or compliance fine? In line with this, the DLP market is […]
Guide: what is data discovery, & why is it essential?
I. Introduction 1. Definition 2. Concepts – Manual – Smart II. Importance III. Processes 1. Data preparation 2. Visual analysis 3. Guided analytics IV. Conclusion Introduction We want to start this article by casting your mind back to the prime days of public libraries. We know that they still exist, but we also know that […]
What are critical data elements (CDE), & why are they so critical for security?
Data protection and data governance are two important facets of every organization’s cybersecurity and compliance strategy. Not only that, but they’re essential to keeping things running. If your people can’t find the data they need, or it’s difficult to use, this could cause a number of problems. Plus, with the advent of both state and […]
Missed-configuration: the MS PowerApps fiasco
When you hear the words: “Microsoft” and “data breach” in the same sentence, chances are your eyes will widen with panic. The ubiquity of Microsoft’s software and hardware means that most organizations and people interact with the brand in one way or another. Whether it’s Teams, Office 365, or Power Apps, Microsoft is everywhere. The […]

